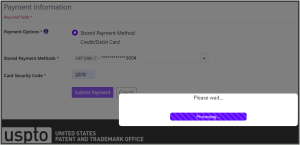
(Update: 23 hours have passed since I opened ticket number 2-01001251 about Patent Center puking on a patent application prepared in Libre Office. Nobody from the USPTO got back to me during these 23 hours. Tomorrow is the priority date on which I need to get this patent application filed. I phoned up the EBC again just now, and was told “the only other thing I can recommend is just use [Microsoft] Word.” See followup blog article.)
The USPTO’s non-DOCX surcharge is now rearing its ugly head again. Let’s see if, between now and tomorrow, May 15, 2026, the USPTO people in charge of the non-DOCX penalty provide decent software support for the filing of a new patent application that was prepared using a word processor that is not Microsoft Word. Watch this blog to see how the USPTO handles this defect in Patent Center. Continue reading “USPTO’s non-DOCX surcharge rears its ugly head again”