If you have a computer that runs Microsoft Windows 10, you probably did a pretty substantial Windows update within the past few months — the kind of update that requires two or three long periods of time during which the computer counts slowly up a percentage, reboots itself, and solemnly warns you not to unplug the computer or power it down or allow the battery to run down during the next few minutes. After this update, you may have started noticing warnings when you connect to some wifi networks. The warning says something like:
This wifi network uses an older security standard that is being phased out. We recommend using a different network.
It wouldn’t be so bad except that likely as not, this warning is happening when you are connected to your own wifi network! So what the heck are you supposed to do about this?
It turns out that the Windows warning is unnecessarily vague. There are exactly two things that your Windows might not like about the wifi network that you are connected to. (They are called “WEP” and “TKIP“.) When the software in your computer pops up this warning, the software does not, however, say which of the two things prompted this particular warning. It means that if you are going to go looking around in your router or access point to try to figure out how to make this problem go away, you have to go on a treasure hunt. It might be the one thing or it might be the other. It would have been much more user-friendly if Windows were to actually come out and say which of these two offending protocols prompted the particular warning that is on your screen.
Anyway if you want my guess, for every reader of this blog it will turn out that the way to make the warning go away is to turn off TKIP (not turning off WEP). The reason for this is that every reader of this blog has likely known for many years now not to use WEP. Everybody knows that WEP is flawed, and knows not to use it. Every reader of this blog has been using WPA2 instead of WEP for many years now, in his or her wifi router or wifi access point.
So that means the only thing left that you could be doing wrong, without knowing it, is using TKIP.
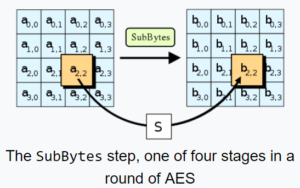
What has been happening in the past few years is that almost all wifi routers and access points seem to have a default setting on the type of encryption that is going to be used on the wifi network, namely “auto”, meaning an automatic negotiation of either of two encryption protocols TKIP and AES. AES is the more recently developed encryption protocol, and as of the present day nobody has found weaknesses in it. By comparison it turns out that weaknesses have been found in TKIP. (The figure above shows part of the AES computations.)
The reason for “auto” is, I guess, that some older pieces of equipment predate the development of the AES standard and only know how to do TKIP. So for the past few years the designers of most wifi routers and access points have been designing their systems to try to negotiate an AES connection when possible, and to use TKIP only as a last resort.
This, however, runs afoul of the pickiness of this latest version of Windows 10. This latest version of Windows 10 takes offense if the wifi router or access point is even willing to do TKIP even if nearly always the actual outcome is that the connection that gets negotiated is AES.
I suppose although this is a bit paternalistic on the part of Microsoft, it is the right thing to do. It forces us to turn off the “auto” setting that would permit our router or access point to do either TKIP or AES. Instead, it forces us to configure our router or access point to only be willing to do AES.
And that’s what you gotta do, seems to me.
Of course this means that once you turn off “auto”, you might run into some old computer or other piece of equipment that cannot connect any more to your wifi network. It would be some piece of equipment that is so old that it only knows how to do TKIP but does not know how to do AES. It would then be up to you to decide what to do about that.
Have you encountered this warning? Did you turn off TKIP to make the warning go away? Please post a comment below.
