Recently I blogged with a recommendation that readers migrate their $40 or $55 per month landlines to VOIP lines that cost as little as 85¢ per month. In response, alert reader and Portuguese and European patent attorney Luís Ferreira asked:
What about security? SIP communications are not normally encrypted?
His questions are good questions. Here are a few partial answers.
A typical SIP communication will have two links — a “trunk” link between the VOIP service provider (such as voip.ms) and your Asterisk telephone switch, and an “extension” link between your Asterisk telephone switch and the physical telephone used by the human user. Each of those links can be separately analyzed for its security. I will discuss this momentarily.
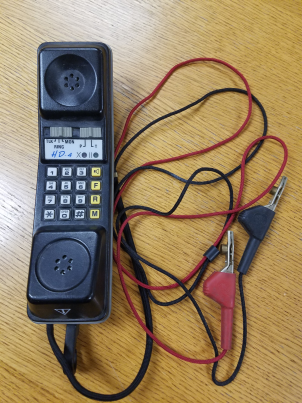
It is also instructive by way of background to consider the security of a legacy landline telephone call. A legacy landline telephone call is strikingly insecure. It is communicated in an analog signal on copper wires which can be easily eavesdropped upon with inexpensive easily obtained equipment such as the “butt set” shown at right.
Now let’s talk about SIP (which stands for “Session Initiation Protocol”). Several things happen when a SIP call takes place. First, the “call setup” happens. These are things like somebody dialing a phone number and the system figuring out whether the called number is busy, and making the phone ring, and detecting if the callee has picked up the handset, and so on. This is all done by means of SIP messages, typically on UDP port 5060 or TCP port 5061. Likewise when a phone call reaches its end, typically with somebody hanging up a phone handset, the voice path needs to be “torn down” and this is also done by means of SIP messages.
When the call setup reaches the point where two people are supposed to talk with each other, the SIP messages negotiate an RTP session between the two endpoints. (RTP stands for “Real-time Transport Protocol”.) All of the audio that is being communicated between the two endpoints is passed by means of RTP packets.
Either or both of these kinds of data message (SIP on the one hand, and RTP on the other hand) has the potential to be eavesdropped upon.
As for the SIP messages (used for setting up and tearing down talk paths), there are three choices for the kind of data packets being used — UDP, TCP, and TLS. The third choice, TLS, uses encryption. If TLS is employed, this makes it very hard for an eavesdropper to make any use of the intercepted SIP data packets.
As for the RTP packets, there are two choices — RTP and SRTP. The latter uses enc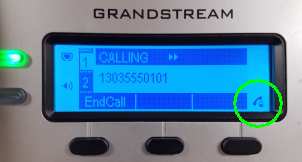 ryption. SRTP makes it very hard for an eavesdropper to make any use of the intecepted RTP packets.
ryption. SRTP makes it very hard for an eavesdropper to make any use of the intecepted RTP packets.
When we set up our new Grandstream PBX recently, we configured it to use TLS and SRTP wherever possible. You can see at right a little “lock” icon on the display screen of one of our telephone extensions, which indicates that the telephone call that is taking place is protected by SRTP.
As I mentioned above, a typical SIP telephone call has two segments — a first segment from the VOIP server provider to our PBX, and a second segment from our PBX to the end-user’s telephone extension. As for the second segment, we control both ends of the segment because we own the PBX and we own the extension telephones. So we are able to force it that this segment is encrypted both as to SIP packets and as to RTP packets.
What I have found is that most VOIP service providers do not support TLS or SRTP. It means that a dedicated eavesdropper, if making use of sufficiently sophisticated equipment, could intercept packets between our office and the VOIP service provider, and could reconstruct the telephone calls.
Of course what would be desirable is if more VOIP service providers were to support TLS and SRTP. Between now and when that happens, the calls could be eavesdropped upon at points between our office and the facilities of the VOIP service provider, although not nearly so easily as eavesdropping upon legacy landline telephone calls.

Thank you for the in-depth post! You are quite right, landline security is most of the times appalling. At home, the junction box is in the street and can be opened by anyone, no special keys required. At work, from an initial check, it seems our current provider already uses voip for providing service to our pbx – I have to check further, but it seems we were already using voip without knowing it!
VoIP has been around since the mid-1990’s, but hosted VoIP has not been a viable option until probably less than 10 years ago. The reason was due to lack of ample, reliable, cost-effective bandwidth. Now it’s been widely used everywhere. And thanks for the great share about Voip Communications.