(Followup — USPTO did the right thing and stopped publishing IP addresses. See this blog post.)
Those who read the previous posting, about the need for USPTO to implement SSL and PFS on all of its outward-facing e-commerce systems, will have heard of the suspicion that a company is eavesdropping on TESS sessions and then uses the results of the eavesdropping in emailed sales pitches. The alert reader will wonder how it is that such an eavesdropper would be able to figure out what email address to use to reach someone at an otherwise seemingly random IP address. The answer is that the US Trademark Office needs to stop publishing IP addresses linked to email addresses.
In an aspect of breathtakingly stupid system design, USPTO designed TEAS so that the IP address of the filer is posted as a matter of public record in the TSDR records. So for example look at the TSDR record for US trademark registration number 4525914 for the mark “Google”. This application was filed by Monique Liburd. And toward the bottom of the application, USPTO has made it a matter of public record that when she did it, s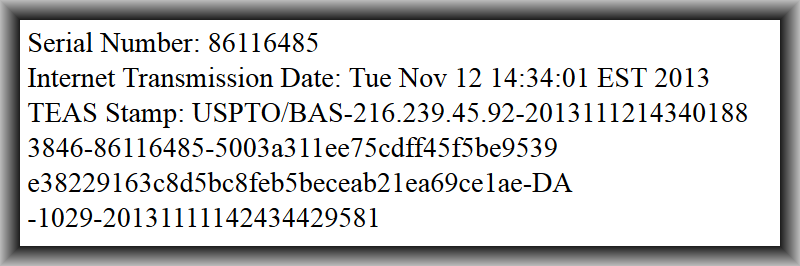 he was at IP address 216.239.45.92. TSDR also reveals to the public the email address that USPTO is invited to use to communicate with Ms. Liburd.
he was at IP address 216.239.45.92. TSDR also reveals to the public the email address that USPTO is invited to use to communicate with Ms. Liburd.
This then permits an eavesdropper to sniff the Internet looking for web traffic to TESS, that happens to originate from that IP address. When it intercepts a web session from that IP address that searched for, say, GNOOGLE, then the eavesdropper knows it was probably Ms. Liburd or at least someone in her office. It can then send an email to that email address that makes a sales pitch that makes use of the content of the web session, name-dropping “GNOOGLE” as part of the sales pitch.
USPTO should never have done this publishing of IP addresses of USPTO customers in a way that links the IP address to a particular customer. It should stop now, and it should go back and redact the IP addresses from existing public records in TSDR.

Carl, thank you for this analysis. Have there been any developments in terms of the USPTO addressing the issue?